The Enigma machine, a complex encryption device employed by Nazi Germany during World War II, presented a formidable barrier to Allied intelligence efforts. Originally conceived in the 1920s by Arthur Scherbius, the machine’s design seemed impenetrable, combining intricate rotors and an array of settings that transformed military communications into seemingly uncrackable codes. However, the codebreakers stationed at Bletchley Park, including the prominent mathematician Alan Turing, utilized innovative methods to challenge this illusion of security.
The contributions of these codebreakers were pivotal, as they developed the Bombe, an electromechanical device capable of rapidly testing various configurations of the Enigma machine. Their success in breaking the codes allowed the Allies to intercept vital information, significantly influencing key operations such as D-Day and the Battle of the Atlantic. The legacy of these efforts, which not only shortened the war but also laid the groundwork for modern computing and cybersecurity, highlights the profound impact that intelligence work has had on the course of history.
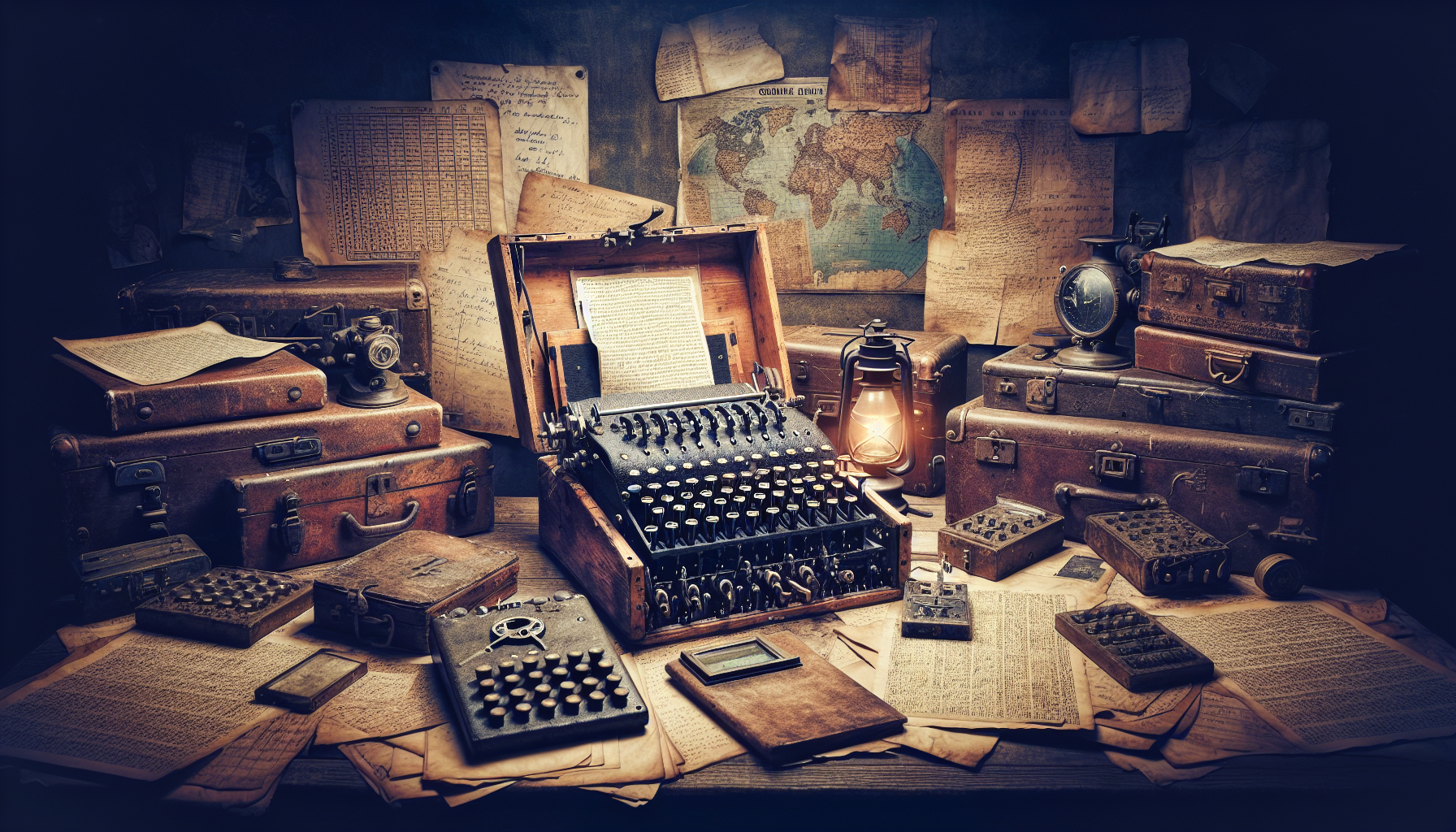
The Enigma Machine

Origins and Invention
The Enigma machine first emerged in the landscape of the 1920s, a product of ingenuity designed by the German engineer Arthur Scherbius. Initially intended for commercial use, this complex device was quickly repurposed by military factions within Germany who recognized its capacity for encrypting sensitive communications. The design bore a striking resemblance to a typewriter, incorporating a series of rotors and electrical connections that together scrambled messages into sequences that seemed impenetrable. Each pressing of a key initiated a rotation of these rotors, creating a staggering array of potential configurations for encoding messages. For the German military, the confidence in the machine’s security was unwavering; they regarded their coded communications as effectively unbreakable, counting on the vast number of possible settings to ensure confidentiality.
Mechanics of Encryption
To understand the workings of the Enigma machine is to delve into the intricacies of mechanical encryption. The device deployed a method known as polyalphabetic substitution, involving multiple alphabets that changed with each letter typed. Specifically, the rotor system comprised several rotating disks, with each disk capable of wiring electrical signals to different letters of the alphabet. With each key press, the rotors advanced, altering the state of the encryption with an extraordinary number of configurations—over 150 quintillion. This complex dance of cogs and inputs created an enigma so profound that it tantalized even the most knowledgeable cryptologians of its time. Such complexities gave rise to the belief that the machine’s encoded messages were beyond the reach of both cryptanalysis and human ingenuity.
Perceived Security and Complexity
The confidence placed in the Enigma’s security hinged not just on its mechanical sophistication, but also on the growing cultural belief in the infallibility of technology. German command viewed the cryptographic system as a vital asset, essential for maintaining secrecy in military operations. Eclipsed by the sheer operational complexity of the Enigma, the German military underestimated the potential for human intellect to deconstruct the riddle. Thus, the dual layers of perceived security—both from the machine’s complexity and a cultural assumption of technological supremacy—conferred a false sense of invulnerability upon those who relied on it for military communications.
The Role of Polish Cryptologists
Early Breakthroughs in the 1930s
Long before the war reached its cataclysmic heights, Polish cryptologists were already making significant strides in breaking the Enigma codes. A pioneering group led by mathematicians Marian Rejewski, Jerzy Różycki, and Henryk Zygalski had successfully deciphered early versions of the Enigma machine by exploiting flaws within its design. By the mid-1930s, these scholars had formulated a mathematical framework that facilitated their ability to convert encrypted messages back to their plaintext form. Their groundbreaking work included the creation of the first known cryptographic tools designed to analyze Enigma transmissions, laying foundational knowledge that would prove invaluable to the Allies.
Collaboration with Allied Forces
As the shadows of war loomed over Europe, the Polish cryptologists recognized the critical necessity of sharing their insights with Allied forces. In 1939, just before the German invasion of Poland, these cryptologists passed on crucial information regarding the Enigma’s mechanisms and provided training to British and French counterparts on how to implement their techniques. This collaborative spirit fostered a cross-pollination of ideas, preparing the groundwork for the extensive efforts that would soon unfold at Bletchley Park.
Impact of Poland’s Invasion
When Germany invaded Poland in September 1939, the Polish cryptologists faced the imminent threat of destruction, yet their contributions would resonate far beyond their own borders. With Polish intelligence in possession of vital knowledge concerning the Enigma machine, the transition of that intelligence to British authorities became a beacon of hope for the Allied forces. Despite the disarray brought on by war, the remnants of Polish ingenuity provided a critical lifeline to those committed to the task of codebreaking.
Bletchley Park: The Codebreaking Hub
Establishment of Bletchley Park
Amid the backdrop of World War II, Bletchley Park emerged as a veritable sanctuary for intellect and cryptographic analysis. Located in Buckinghamshire, England, this estate transformed into a clandestine beehive of mathematicians, linguists, and engineers united by a singular purpose: to decipher the secrets encoded by devices like the Enigma. Bletchley Park housed the Government Code and Cypher School (GC&CS), wherein a diverse array of talents converged, each bringing unique insights to the monumental task of breaking encrypted German communications.
Diversity of Expertise
The personnel at Bletchley Park epitomized a remarkable cross-section of society. Comprising women and men from various academic, linguistic, and engineering disciplines, the workforce exemplified the rich tapestry of expertise necessary for cryptanalysis. The contributions ranged from mathematicians applying complex theories to linguists interpreting intercepted messages. This eclectic mix fostered an environment where creativity met analytical rigor, resulting in collaborative efforts that would yield profound breakthroughs in the field of cryptography.
Culture and Environment of Codebreakers
Bletchley Park was not merely a workplace; it represented an amalgamation of ingenuity and camaraderie amid the pressing pressures of war. The culture of the codebreakers was grounded in secrecy and mutual respect. Within the atmospheric huts dispersed throughout the estate, camaraderie flourished, and friendships blossomed under the heavy cloak of confidentiality. It was here, amid the tightly-knit community of bright minds, that permanence met urgency, driving an abiding commitment to decryption that changed the course of history.
Notable Codebreakers at Bletchley Park
Alan Turing: The Pioneer
Among the pantheon of Bletchley Park’s codebreakers, Alan Turing stands as a towering figure—a pioneer whose intellect and innovative spirit defined the era. Turing’s theoretical work in mathematics and logic laid the groundwork for modern computing, but it was his tireless efforts against the Enigma machine that marked his most significant contributions during the war. Turing’s conceptualization of the Bombe, an electromechanical device designed to expedite the decryption process, effectively revolutionized codebreaking, allowing the Allies to outpace the German military in intelligence gathering.
Joan Clarke’s Contributions
Joan Clarke’s role at Bletchley Park serves as a testament to the diverse contributions of women in a predominantly male environment. As a mathematician and cryptanalyst, Clarke was integral to the success of Turing and his team. Her inventive thinking and collaborative spirit catalyzed significant advancements in the decryption processes. Clarke’s work exemplified the dedication and capability that women brought to Bletchley, challenging prevailing norms and forging a path for future generations of women in STEM fields.
Gordon Welchman’s Innovations
Gordon Welchman was another luminary at Bletchley Park, whose innovations enhanced the efficiency of codebreaking efforts. His development of the “diagonal board” significantly streamlined the process of handling Enigma codes, allowing cryptanalysts to sift through combinations with greater speed. Welchman’s pragmatic approach to problem-solving further enriched the collaborative climate at Bletchley, showcasing how individual contributions could ripple into significant collective success.
The Development of the Bombe
Concept and Design
The creation of the Bombe machine was a pivotal chapter in the Bletchley codebreaking narrative. Driven by the limitations of manual code analysis and the staggering complexity of the Enigma, Alan Turing and his team conceptualized the Bombe. Its design, while mechanical, was rooted in sophisticated mathematical principles. The Bombe exploited the structural weaknesses of the Enigma system, particularly its reliance on repeated keys in messages. Turing’s vision translated abstract calculations into a tangible device that could simulate the Enigma’s operations, encompassing millions of possible settings and iterations.
Operational Mechanism
The operational mechanics of the Bombe were as intricate as they were revolutionary. Each Bombe machine employed a series of interconnected rotors, enabling it to run through the myriad possible configurations of the Enigma’s settings efficiently. By comparing inputted plaintext with suspected ciphertext, the device drastically reduced the time frame necessary for decryption. Rather than relying on human endurance to analyze permutations, the Bombe brought the promise of speed to bear on an almost unfathomable computational challenge.
Significance in Decryption Efforts
The significance of the Bombe in the Allied war effort cannot be overstated. The ability to break Enigma codes in a matter of hours, rather than weeks or months, transformed the landscape of military intelligence. The insights gleaned through the efforts of Turing and his Bombe team translated into actionable intelligence on German movements, troop deployments, and naval strategies. In a war where information was power, the Bombe emerged as the key to unlocking encoded messages, altering the trajectory of conflict.
Understanding ‘Ultra’ Intelligence
Definition and Scope of Ultra
“Ultra” intelligence refers to the classified information obtained from decrypted German communications, primarily acquired through the efforts at Bletchley Park. The term encapsulated high-level insights that were crucial for wartime strategy and tactical planning. Ultra intelligence provided the Allies a distinct advantage, equipping them with knowledge that turned the tides of specific battles, supported strategic decisions, and shaped the broader operational framework against Axis forces.
Sources of Ultra Intelligence
The sources of Ultra intelligence were diverse, encompassing a wealth of intercepted communications that spanned various military operations. These insights were derived not only from the decryptions of the Enigma machine but also from other intelligence-gathering technologies—such as intercepting radio messages and analyzing captured documents. The volume and variety of signals processed culminated in an unparalleled reservoir of information that proved vital to the Allied war effort.
Impact on Military Strategy
The impact of Ultra intelligence on military strategy was profound and multifaceted. With access to real-time data regarding enemy movements and intentions, Allied commanders were enabled to craft operations that were both proactive and reactive. Perhaps one of the most notable instances was the D-Day invasion, where Ultra intelligence played a crucial role in informing troop deployments and strategies. By disseminating valuable insights propelled by Ultra, the Allies gained the upper hand—foreseeing and countering German maneuvers with remarkable efficacy.
Key Operations Aided by Ultra

D-Day: The Invasion of Normandy
The Allied invasion of Normandy on June 6, 1944, stands as a testament to the extraordinary capabilities of Ultra intelligence. With decisive insights regarding German troop placements and defensive strategies, Allied commanders orchestrated an unprecedented amphibious assault. The operational timing and execution of D-Day were intricately planned based on Ultra intelligence, which informed leaders about the enemy’s fortifications along the coast. The invasion not only marked a significant turn in the war but also highlighted the strategic importance of securing reliable intelligence.
Battle of the Atlantic: U-boat Campaigns
Ultra intelligence significantly impacted the Battle of the Atlantic, as it enabled the Allies to intercept and monitor German U-boat activity. Through decryptions, intelligence units were able to track U-boat formations, predict attacks on merchant shipping, and formulate counter-strategies to protect vital supply routes. The dynamic responsiveness afforded by Ultra intelligence mitigated losses and ensured the continued flow of resources essential for sustaining military efforts on both the European and Pacific fronts.
Critical Role in Other Military Engagements
The contributions of Ultra intelligence extended beyond the pivotal operations of D-Day and the Battle of the Atlantic; its influence permeated other critical military engagements throughout the war. From the North African campaigns to the battles on the Eastern Front, the insights garnered through ultra-secret intelligence reshaped tactical decisions. Such intelligence not only bolstered military operations but also instilled a growing sense of confidence among commanders who understood the strategic advantage that intelligence could confer in a global conflict.
Challenges Faced by Codebreakers
Mental and Emotional Strain
While the achievements at Bletchley Park are often celebrated, the mental and emotional toll on codebreakers was profound and often overlooked. The pressure to deliver timely decryption results posed significant psychological challenges. Many individuals faced constant fatigue, long hours, and the weight of a world war hanging on their successes. The burden of secrecy often compounded these stresses, isolating them psychologically from their families and communities as they endeavored to maintain the veil over their revolutionary work.
Secrecy and Post-War Effects
In the aftermath of World War II, the culture of secrecy surrounding Bletchley Park had lasting implications for its codebreakers. Many contributors to the war effort were sworn to confidentiality, inhibiting their ability to share their experiences publicly even years after the conflict ended. This led to a collective obscurity despite their pivotal roles in shaping the outcome of the war. The extraordinary contributions of these individuals remained hidden, evolving into a narrative of both triumph and sacrifice.
Technical Limitations and Failures
Though the breakthroughs at Bletchley Park marked a significant advancement in cryptography, codebreakers faced daily technical limitations and failures in their work. Enigma’s continual adaptations meant that new versions required constant recalibration of their decryption techniques and tools. Challenges also arose from the limitations of human cognition when confronted with the staggering volume of intercepted messages. These technical hurdles necessitated collaboration and ingenuity, with the ever-present possibility of failure demanding both resilience and adaptability.
Legacy of World War II Codebreakers
Influence on Modern Computing
The legacy of World War II codebreakers resonates powerfully in the context of modern computing. Figures like Alan Turing laid foundational principles of computer science and artificial intelligence, influencing developments that emerged in subsequent decades. If Turing’s work encapsulated the early confluence of mathematics and computation, then the methodologies employed at Bletchley Park paved the way for the architecture of today’s digital landscape. The act of codebreaking became a precursor to many operations that define contemporary computing and cybersecurity.
Advancements in Cryptography
The contributions of the WWII codebreakers also catalyzed crucial advancements in the field of cryptography itself. Their innovative approaches to encryption and decryption redefined the framework utilized in subsequent generations of cryptographic theory and practice. As cryptographic systems evolved, the principles cultivated at Bletchley Park continued to inform methodologies aimed at securing communications across various domains. The legacy of these codebreakers persists in algorithms and protocols that underpin secure communication in the digital age.
Cultural Recognition and Representation
As time progressed, the narrative surrounding the codebreakers began to shift from obscurity to recognition. Cultural representations in literature, film, and education have sought to illuminate the lives and contributions of those who dedicated themselves to the codebreaking mission. Furthermore, the acknowledgment of their work has catalyzed discussions around issues of intellectual labor, gender equality, and the ethical dimensions of intelligence gathering, ensuring that their sacrifices and intellect are celebrated.
Conclusion
Reflection on the Importance of Codebreaking
The story of codebreaking during World War II encapsulates the interplay of intellect, technology, and human endeavor at a critical juncture in history. The work done at Bletchley Park and by cryptologists around the globe serves as a vivid reminder of how encryption and decryption can shape global events. The pursuit of knowledge, whether through mathematics or collaboration, reflects a profound commitment to preserving freedom in the face of tyranny.
Enduring Lessons from WWII Codebreakers
As contemporary society grapples with new challenges in cybersecurity and cryptography, the lessons derived from WWII codebreakers remain salient. Their experiences offer us a blueprint for collaboration, the significance of adaptability in problem-solving, and the ethical considerations that accompany intelligence work. In recognizing the humanity behind these technological triumphs, we cultivate a deeper understanding of the values we must uphold as we advance into an increasingly digitized future.
Call for Continued Innovation in Security
In an age where information is both a weapon and a shield, the call for continued innovation in security is unwavering. The historical context provided by the contributions of codebreakers should serve as a catalyst for contemporary technological advancement. As we strive to safeguard our communications and autonomy, may we remain inspired by the resilience and intellect of those who came before us, fostering a spirit of innovation that propels us toward a more secure future.
